Gallagher Access Controllers (27)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
- Make
- Gallagher
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasises the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
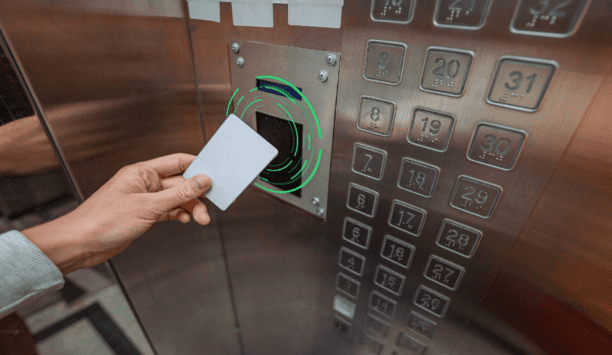
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Latest Gallagher Security (Europe) Ltd news

Gallagher Security is thrilled to celebrate Jeff Ogborn, Senior Solutions Engineer, as a recipient of the 2025 Security Innovator Award, the industry’s only recognition progr...

Gallagher Security has now announced the appointment of Jake Kearns as National SMB and Perimeter Manager. Jake’s role is dedicated to supporting Channel Partners and...

A system's lifecycle is the journey it takes from planning and design through to decommissioning. Considering the entire lifecycle of a system can encourage integrators and end use...
Related white papers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge
Trending topic articles
Absolute Security, a pioneer in enterprise cyber resilience, has launched its Rehydrate technology on general availability. Enterprises with business operations that have been stopped by Windows PCs...
MacGuard Security Advisors proudly announces its advisory role in the recently announced acquisition of Gallaher & Associates (Gallaher) by Zeus Fire and Security (Zeus), a portfolio company of Ba...
360 Vision Technology has launched a revolutionary ‘Digital Twin’ online 3D virtual environment that is set to transform how customers, consultants and partners engage with the brand&rsquo...
Genetec Inc., the global pioneer in enterprise physical security software, announced new intelligent automation (IA)-powered investigation capabilities in Security Center SaaS to help operators quickl...
Blackline Safety Corp., a global pioneer in connected safety technology, announced a new $1.8 million contract with a major North American water and wastewater utility provider based in California.&nb...
The sheer volume of smart locks, lock management systems, connected readers and an increasing array of Internet of Things (IoT) devices complicates the issuance and management of certificates that are...
inforcer, a pioneer in Microsoft-focused multi-tenant management for Managed Service Providers (MSPs), announced its selection as a Microsoft partner in enabling #IntuneforMSPs. The global initiative...
INTERSCHUTZ 2026 (1-6 June) is already shaping up to deliver a wealth of highlights. For the first time, the world’s major trade fair for firefighting, rescue, and civil protection will feature...
OPSWAT, a global pioneer in critical infrastructure protection (CIP), announced the opening of its international briefing centre and state-of-the-art cybersecurity lab in London, marking a significant...
DigiFlight and its subsidiary, Camelot Secure, a revolutionary cybersecurity company, announced that Loilette Loderick, Network Forensics Analyst, has been named a finalist for the prestigious TechWom...
Hikvision has announced the integration of its AcuSeek AI-powered video analytics into two key platforms: HikCentral Professional and Hik-Connect 6. This breakthrough technology transforms the...
Cohesity and Semperis announced a new product, Cohesity Identity Resilience, powered by Semperis, to defend enterprises’ critical identity infrastructure, including Microsoft Active Directory as...
At a hearing on Sept. 16, 2025, Brett Feddersen, Chair of the Security Industry Association (SIA) Drone Security Subcommittee and vice president for strategy and government affairs at D-Fend Solutions...
At GSX 2025, September 29 – October 1, Bosch Video Systems will introduce products and solutions designed to significantly enhance situational awareness for customers. Visitors to the GSX boot...
Ping Identity, a pioneer in securing digital identities for the world’s largest enterprises, announced a new AI framework designed to close the trust gap created by the rise of AI agents, along...
Artificial Intelligence in Security
DownloadElevating security through multi-sensing solutions and large-scale AI
DownloadOpen credential standards and the impact on physical access control
DownloadCombining security and networking technologies for a unified solution
DownloadWhat is a universal RFID reader?
Download









































